Risk Management Enterprise for Dummies
Wiki Article
The 9-Minute Rule for Risk Management Enterprise
Table of ContentsOur Risk Management Enterprise PDFs4 Easy Facts About Risk Management Enterprise ExplainedUnknown Facts About Risk Management Enterprise
Control who can check out or edit these elements by establishing specific gain access to rights for specific customers, making certain details security and tailored use. Permits users to tailor their user interface by picking and preparing important data components. Supplies an individualized experience by permitting personalization of where and just how information aspects are displayed.It enables access to real-time integrated information instantaneously. Centers can use detailed data knowledge for quicker and much more educated decision-making.
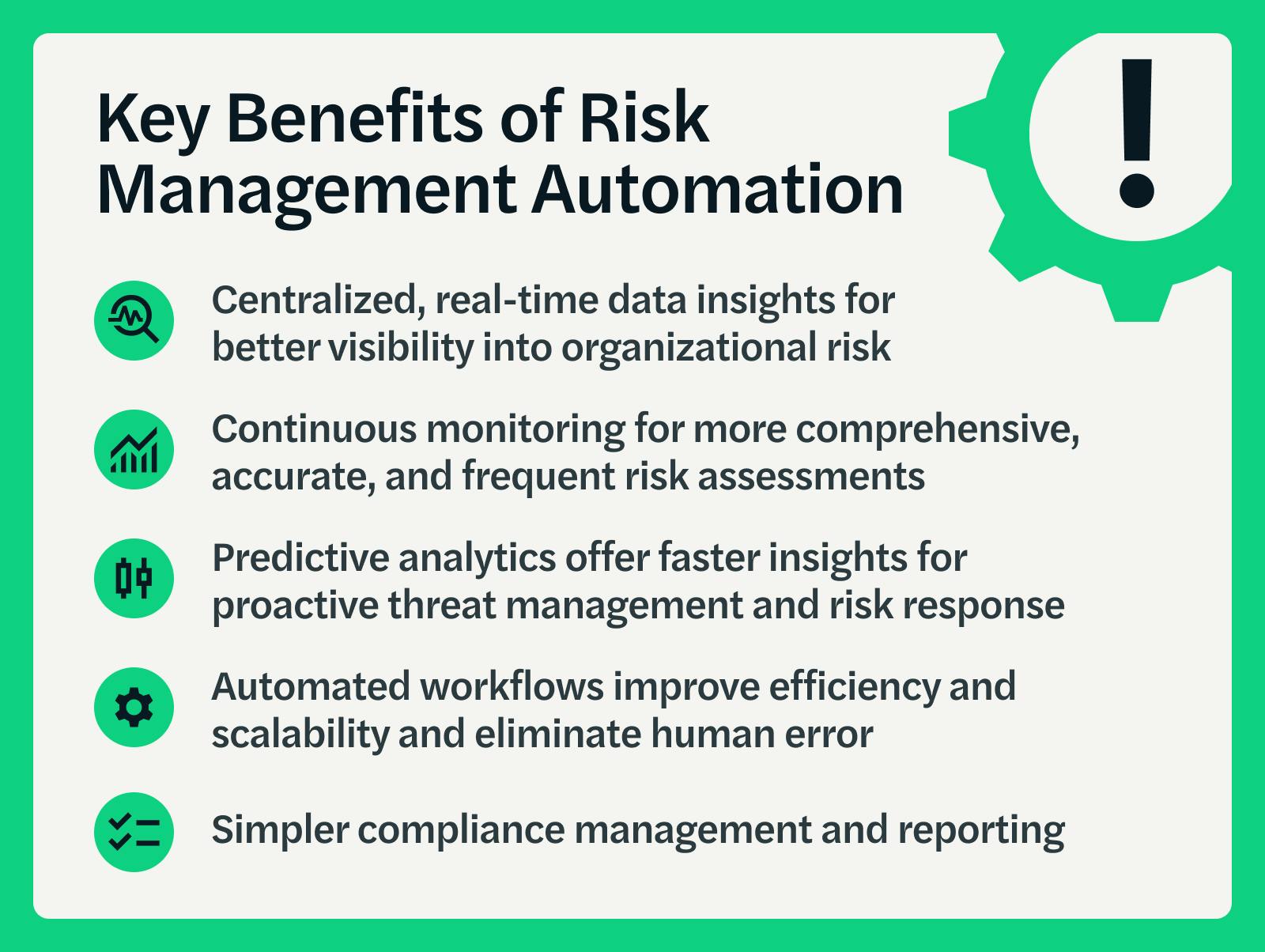
Diligent is a threat administration software that allows maximizing performance, and enhances growth. It likewise assists keep an eye on threats with ERM software that includes integrated analytics and adapts to your service needs.
The Single Strategy To Use For Risk Management Enterprise
Streamlines the process of accumulating threat data from different components of the organization. Gives management and the board with real-time threat understandings. Usage ACL's sophisticated analytics to identify risk patterns and forecast threats.This permits business to catch danger insights and warnings in the third-party content vendor's safety and security report. This allows for conserving risk assessments as auditable papers. It additionally permits exporting them as PDFs. To complete the process companies can complete a view publisher site reassessment day. Makes it possible for firms to record and record risk insights and red flags in third-party vendor security reports.
Identifying threats in advancement helps a center plan for audits. It additionally decreases threat via structured conformity and risk administration. Due to this facilities will not need to juggle various systems for more risk tracking. The individuals of Hyperproof can streamline risk management in one place. It can aid collect and track all your risks in the Hyperproof danger register.
It supplies fast access to necessary details and documentation. This guarantees the security of Active proof circumstances by enabling multi-factor verification (MFA) using authenticator applications such as Google Authenticator, Microsoft Authenticator, or Authy.
A Biased View of Risk Management Enterprise

It provides top-tier safety and security attributes to guard delicate data. This threat administration software is a best tool for centers looking to repair unnecessary problems or threats.
Individuals can additionally utilize the AI-powered devices and pre-existing content to produce, examine, prioritize, and address threats effectively. Improves the process of setting up and inhabiting risk registers.
Report this wiki page